Features
Dashboard
Sigma’s Dashboard provides a unified operational view across all connected compute environments, cloud providers, and automation modules. It surfaces real-time infrastructure health, global resource distribution, cost insights, and AI-driven recommendations — all within a single interactive workspace.
Note
The Dashboard automatically aggregates data from all Sigma modules (Compute, VDI, ITSM, AI, and Orchestration) and refreshes continuously without manual reloads.
Global View
Visualize every connected region, datacenter, and cloud provider on a dynamic, interactive map.
Key Features
Geo-Aware Map: Displays all active resources across AWS, Azure, GCP, VMware, and OCI.
Provider Outage Overlay: Integrates with public cloud status APIs to highlight current or recent outages by region.
Resource Density Heatmap: Uses color gradients to show VM, storage, and network concentration globally.
Real-Time Status Indicators: Green/yellow/red icons reflect current availability, performance, or maintenance states.
Drill-Down Navigation: Click any region to open an environment-level summary (hosts, cost, compliance, tickets).
Tip
Hover over any region marker to see active VMs, provider status, cost trend, and recommended next actions.
Actionable Insights
AI-powered analytics surface the most impactful operational improvements automatically.
Example Insights
Migration Opportunities: Identify VMs that would benefit from migration to a more cost-efficient or better-performing provider (e.g., move non-critical workloads from AWS to OCI).
Performance Imbalance: Detect uneven load across hosts or datacenters and suggest balancing tasks.
Cross-Cloud Failover Suggestions: Highlight which workloads are unprotected and recommend replication or DR configurations.
Idle Resource Detection: Flag stopped or underutilized VMs with estimated monthly cost savings if decommissioned.
Each insight includes: - Description of the detected condition - Affected resources and estimated impact - Recommended Sigma Action or Task Sequence to resolve it
Important
Insights are generated by Sigma’s internal analytics engine using performance and cost telemetry — no external AI or data export is required.
Cost Optimization
Track spend, forecast trends, and receive automated cost-saving recommendations.
Cost Analytics
Current Spend Overview: Breaks down cost by provider, environment, and resource type.
Savings Recommendations: Highlights potential monthly savings through power scheduling, right-sizing, or storage tier changes.
Forecasting: Projects monthly and annual spend using rolling 30-day averages.
Anomaly Detection: Automatically flags cost spikes caused by unexpected resource growth or configuration drift.
“What-If” Simulator: Model savings by simulating VM migrations or scale-in actions before applying changes.
Note
Cost data is pulled directly from connected provider billing APIs and stored securely. No billing credentials are retained beyond API access tokens.
Trends and History
Monitor key metrics and events over time through Sigma’s interactive charting engine.
Historical Dashboards
Compute Trends: CPU, memory, and storage utilization per environment over custom time ranges.
VDI Trends: User session counts, FSLogix mount times, and host uptime analytics.
Automation History: Completed, failed, and pending Task Sequences with timestamps and outcomes.
Change Impact Visualization: Correlates infrastructure changes (patches, power actions, migrations) with performance metrics.
Tip
All dashboards support filtering by environment, provider, tag, or time period. Charts can be exported as PNG, PDF, or CSV for reporting or governance reviews.
Alerts and Notifications
Receive contextual alerts directly in the dashboard when conditions require attention.
Provider Outages: Real-time notifications of service disruptions from AWS, Azure, or GCP.
Compliance Drift: Triggers when CIS or configuration baselines deviate.
Automation Failures: Summarizes failed actions or scripts with direct links to retry or view logs.
Budget Thresholds: Sends cost alerts when monthly spend exceeds defined limits.
Important
All alerts are integrated with Sigma’s notification system and can be routed to email, Teams, Slack, or ITSM change tickets.
Customization
Tailor the Dashboard to match your role and focus.
Options
Widget Library: Add or remove tiles for compute, cost, or automation metrics.
Saved Views: Create custom dashboard layouts (e.g., Operations, Finance, Security).
Role-Based Access: Restrict or share dashboards by user group.
Dark/Light Themes: Match dashboard visuals with your workspace preferences.
Tip
Administrators can set a default organizational dashboard while allowing users to maintain their personalized layouts.
Compute
Sigma’s Compute module provides a centralized interface for provisioning, managing, and optimizing compute workloads across cloud and on-prem environments.
Note
This module supports multi-cloud and hybrid compute environments including AWS, Azure, VMware, GCP, OCI, and bare metal, with no agent required.
Compute Actions are powerful, one-click automations for operational tasks across your infrastructure. Each action can be executed using different proComputetocols (SSH, WinRM, cloud APIs, etc.) and logs execution results for audit or ticketing systems.
Important
Most Quick Actions support: - Cross-platform execution (Linux/Windows/cloud-native) - AI-generated workflows via natural language input - Real-time output streaming and logging - Change ticket integration (ServiceNow, Jira, etc.)
Scripts
Execute, generate, and govern automation scripts across all connected environments — securely, intelligently, and with full change management visibility.
Sigma’s Scripts module allows engineers and IT operators to run ad-hoc or saved scripts using agentless protocols, or to generate new ones automatically using Sigma’s AI engine. Each execution is tracked with logs, outputs, and ITSM linkage for compliance and audit readiness.
Key Capabilities
AI-Assisted Script Creation: Generate Bash, PowerShell, or Python scripts automatically by describing your intent in natural language. Example: “Restart IIS on all Windows servers in QA” instantly produces and validates a PowerShell script. Scripts can be further refined or parameterized before execution.
Protocol-Agnostic Execution: Run scripts across multiple environments using the most appropriate protocol — SSH, WinRM, VMware Tools, or cloud-native APIs (e.g., AWS SSM, Azure RunCommand). Sigma automatically selects or suggests the optimal transport per target platform.
Real-Time Streaming & Output Capture: Monitor script output live in the browser. Each line is streamed in real time and stored with timestamps for later review or download. Execution results, return codes, and environment details are preserved for post-task reporting.
Reusable Templates: Save commonly used scripts as reusable templates with metadata (category, tags, environment, author). Templates can include parameters, variables, or secrets, and can be version-controlled through Sigma’s internal repository.
Cross-Environment Execution: Target one, many, or all VMs in an environment simultaneously. Sigma manages concurrency, batching, and error isolation so large-scale runs remain stable and auditable.
Change Management Integration
Sigma Scripts are tightly integrated with ITSM workflows and approval policies to ensure every automation action is properly authorized and documented.
Change Ticket Association: Each script execution can automatically reference an existing ServiceNow or Jira change record, or create one on the fly. Sigma includes execution metadata (who ran it, when, where, and what was changed) in the ticket’s notes or attachments.
Pre-Approval & Peer Review: Configurable rules can require approver sign-off or peer validation before execution in production environments. Scripts awaiting approval appear in Sigma’s Pending Changes queue.
Rollback & Snapshot Hooks: Optionally trigger environment snapshots or backups before running potentially disruptive changes. Rollback commands or reverse scripts can be predefined and executed automatically if a task fails.
Change Correlation: Post-execution data (output, logs, and drift deltas) are automatically correlated with change records for compliance tracking and MTTR analysis.
Governance and Security
Role-Based Access Control: Limit script execution to approved users or groups based on environment and impact level.
Execution Policies: Define guardrails like maximum runtime, command whitelists/blacklists, and restricted directories.
Secret Handling: Credentials and tokens are securely injected at runtime via Sigma’s encrypted vault — never exposed in plaintext.
Audit Logging: Every script run records user, timestamp, command, arguments, affected systems, and results.
Immutable Storage: Logs and artifacts are retained per compliance policy and optionally exported to SIEM or ITSM.
AI and Automation Enhancements
Natural-Language to Script: Convert operational requests into validated executable code instantly.
Script Optimization: AI analyzes previous runs for inefficiencies, suggesting cleaner or faster logic.
Anomaly Detection: Machine learning identifies abnormal behavior in output streams or excessive error rates.
Summarization & Context: Sigma generates a human-readable summary for each execution (e.g., “Patched 4 hosts successfully; 1 host failed due to permission error”).
Continuous Learning: The AI adapts over time from approved scripts and patterns, improving recommendations.
Integration and Automation
Task Sequences: Embed script executions as steps in larger workflows (e.g., “Provision VM → Configure Network → Run Hardening Script → Verify”).
Scheduler: Automate recurring scripts (daily, weekly, monthly) with time zone awareness.
API Access: Run scripts or fetch results programmatically via Sigma’s REST or WebSocket APIs.
Notification Hooks: Send execution summaries to Teams, Slack, email, or ITSM when runs complete or fail.
Compliance and Reporting
Execution Evidence: Every script run generates structured evidence (inputs, outputs, version, status, and linked ticket).
Report Exports: Export execution logs as JSON, PDF, or CSV for audits or root-cause analysis.
Metrics Dashboards: View aggregated script activity by user, environment, and success rate.
Drift Awareness: Automatically trigger configuration validation after scripts modify system state.
Note
All Sigma script operations are agentless, idempotent, and change-ticket-aware. They form a core component of the Sigma platform’s “no-code + governance” automation model.
Tip
Use AI-generated scripts for rapid prototyping, then convert them into approved templates to enforce consistency, change traceability, and compliance across teams.
Package Deployment
Configure and deploy software packages across compute instances using Sigma’s powerful no-code interface. This action enables IT teams to define the exact parameters of a software deployment — including installation path, execution flags, and delivery timing — while abstracting platform-specific complexity.
Key Capabilities
Define installation parameters including: - Executable command-line arguments (e.g., /S for silent installs, custom flags) - Target install directory (e.g., C:Program FilesVendorApp or /opt/app) - Environment-specific overrides
Choose push protocol based on the target environment: - SSH for Linux systems - WinRM for Windows systems - Cloud-native mechanisms (e.g., AWS SSM, VMware guest operations)
Upload custom installers (e.g., .msi, .exe, .deb, .rpm, .tar.gz) or link to a remote repository or cloud object store
Schedule deployments for future execution (e.g., after business hours, during maintenance windows)
Track execution status and logs in real time across all targets
Note
Sigma validates package availability, command syntax, and permissions before deployment begins. Failures are captured and correlated to affected hosts with detailed logs for each node.
Tip
Combine Package Deployment with a Task Sequence to automate full onboarding or remediation workflows — e.g., “Install Agent → Apply Config File → Start Service → Notify ITSM.”
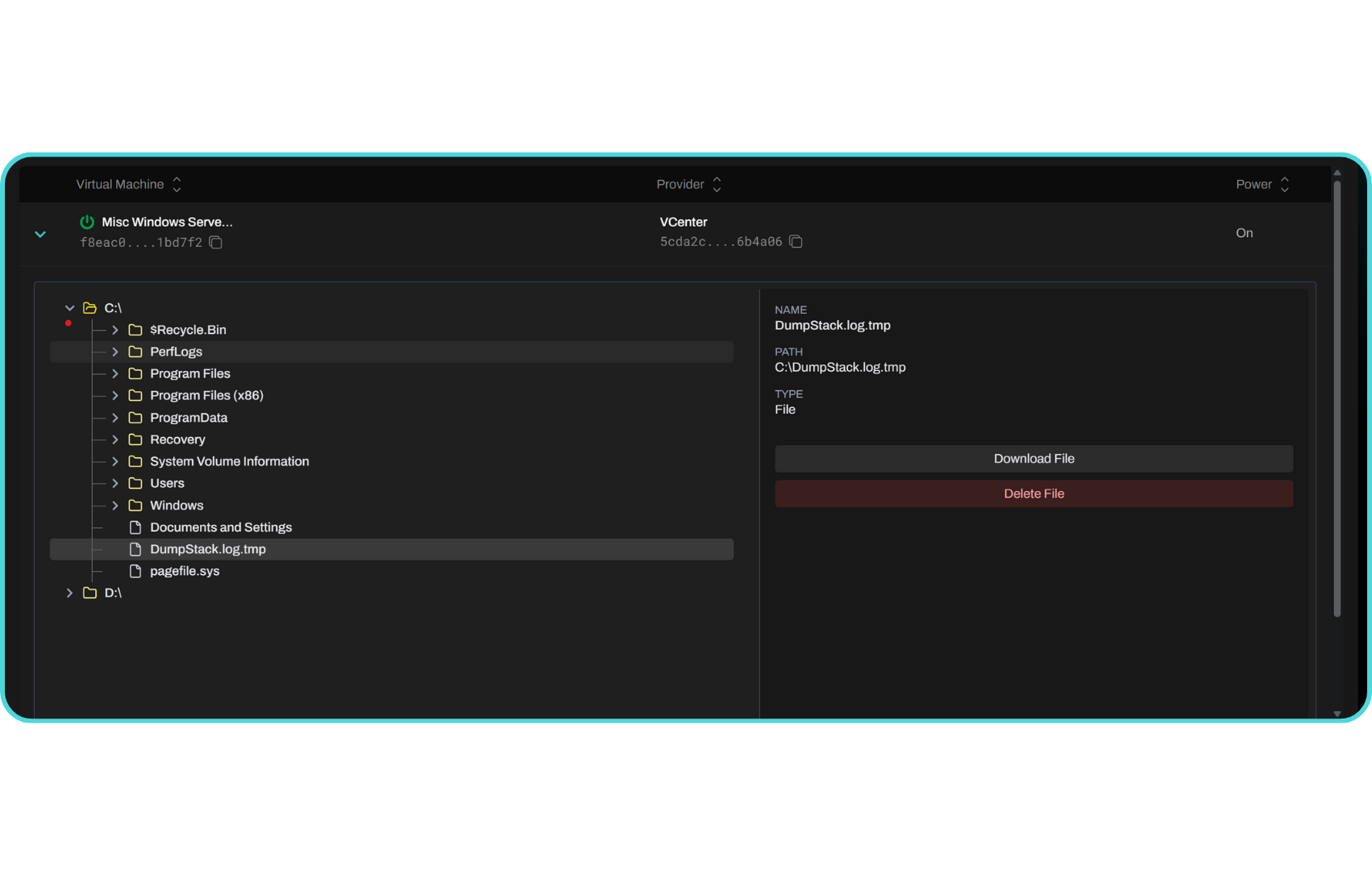
File System
Explore, retrieve, compare, and manage files across any connected compute environment — all directly from Sigma’s web interface.
Sigma’s File System Explorer provides a real-time, agentless view into remote directories, allowing administrators to browse folders, retrieve or delete files, and perform cross-VM comparisons securely over protocols such as WinRM, SSH, or VMware Tools.
Key Capabilities
AI and Automation Enhancements
Sigma integrates AI-driven intelligence to make file management smarter and safer:
Smart File Insight: Automatically classifies uploaded or retrieved files (config, log, binary, script) and suggests recommended next actions (e.g., “Would you like to diff this file against baseline?”).
Automated Drift Detection: Sigma’s ML engine periodically compares known baselines or golden images to current configurations and highlights differences automatically.
Change Summaries: AI generates natural-language summaries of detected changes between versions or across environments (e.g., “Line 12 modified: logging level increased from INFO to DEBUG”).
File Health Analysis: Detects corrupted, truncated, or duplicate files and suggests cleanup or repair.
Security and Compliance
Fully Audited Operations: Every browse, retrieve, upload, and delete action is logged with username, timestamp, target host, and checksum.
Role-Based Permissions: Restrict which users or roles can browse or modify certain directories.
Tamper Protection: File integrity checks ensure downloads or edits match original content hashes.
No Persistent Agent: All operations use secure, short-lived connections via SSH, WinRM, or guest tools — no agent software required.
Integrations and Automation
ITSM Integration: File retrievals or uploads related to change requests can automatically attach to ServiceNow or Jira tickets. Sigma appends context, checksums, and timestamps to each file artifact for compliance records.
Task Sequences: Use file actions within orchestration workflows (e.g., “Upload Config → Validate → Restart Service”). Combine with AI to generate or modify configuration templates automatically.
Event Triggers: Configure policies to trigger alerts or follow-up actions when specific file changes are detected — for example, “Notify Security if /etc/passwd is modified.”
Performance and Reliability
Adaptive Transfer Engine: Uses multi-threaded upload/download logic optimized for latency and throughput. Automatically resumes interrupted transfers and verifies integrity post-transfer.
Cross-Provider Compatibility: Works seamlessly across VMware, AWS, Azure, OCI, and on-prem hosts without requiring shared storage.
Large File Support: Stream files of any size directly to and from Sigma’s backend with chunked compression and encryption.
Summary
Sigma’s File System module replaces traditional manual file operations with a secure, auditable, and AI-assisted explorer — allowing teams to browse, compare, retrieve, and synchronize files across any number of virtual machines in real time, with zero agents and full compliance visibility.
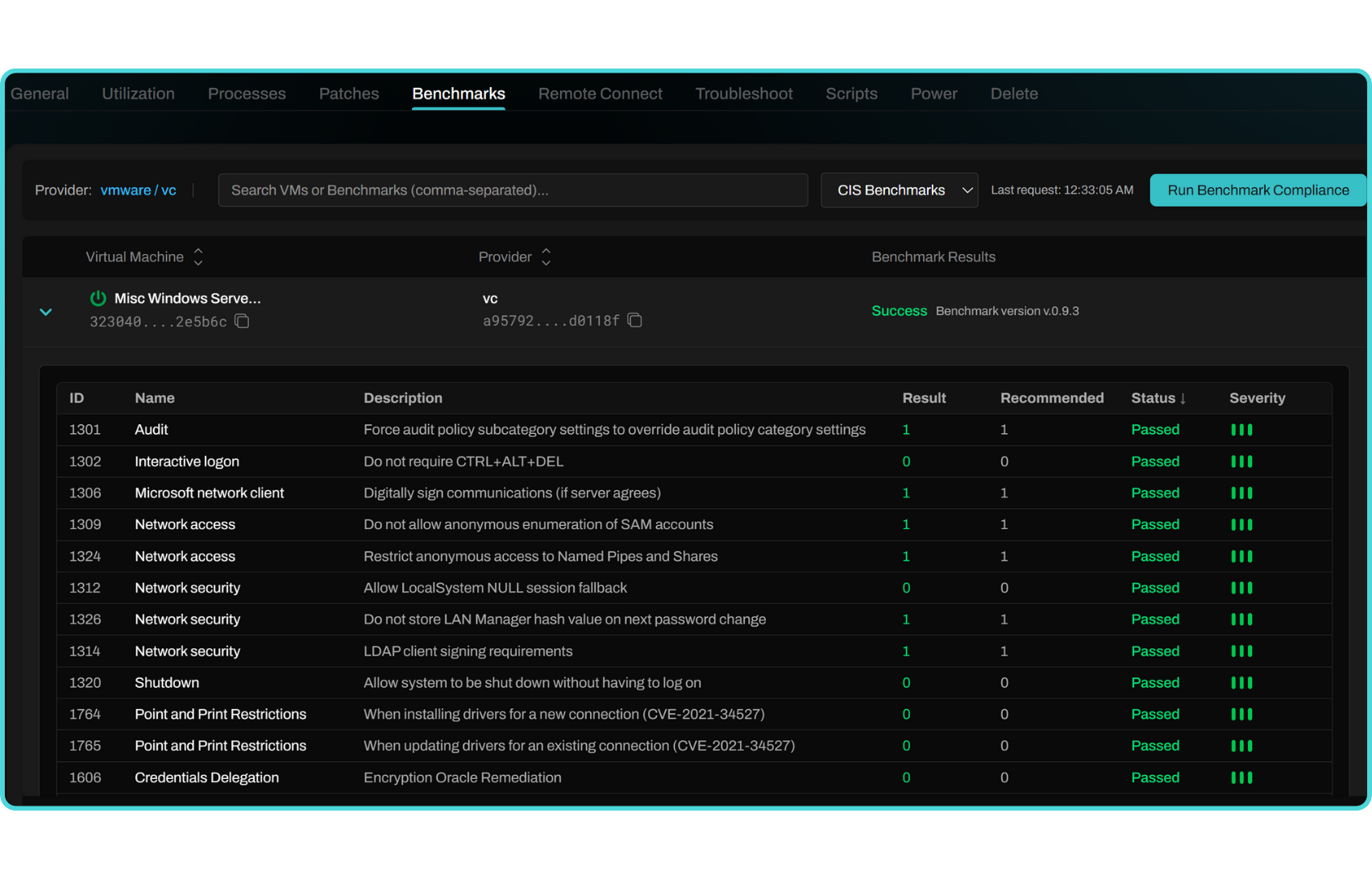
CIS Benchmarks
Output
Per-rule pass/fail with evidence, rationale, and expected state
Risk scoring (overall and category/benchmark family)
Remediation guidance (CLI, GUI, or Sigma script template)
Trend lines (daily/weekly) and drift delta since last scan
Note
Results can be written back to ITSM change/incident records (ServiceNow/Jira) with evidence attachments and approver notes.
Tip
Export reports as PDF, CSV, or JSON for audits. Use scheduled scans and alerting when high-risk controls regress.
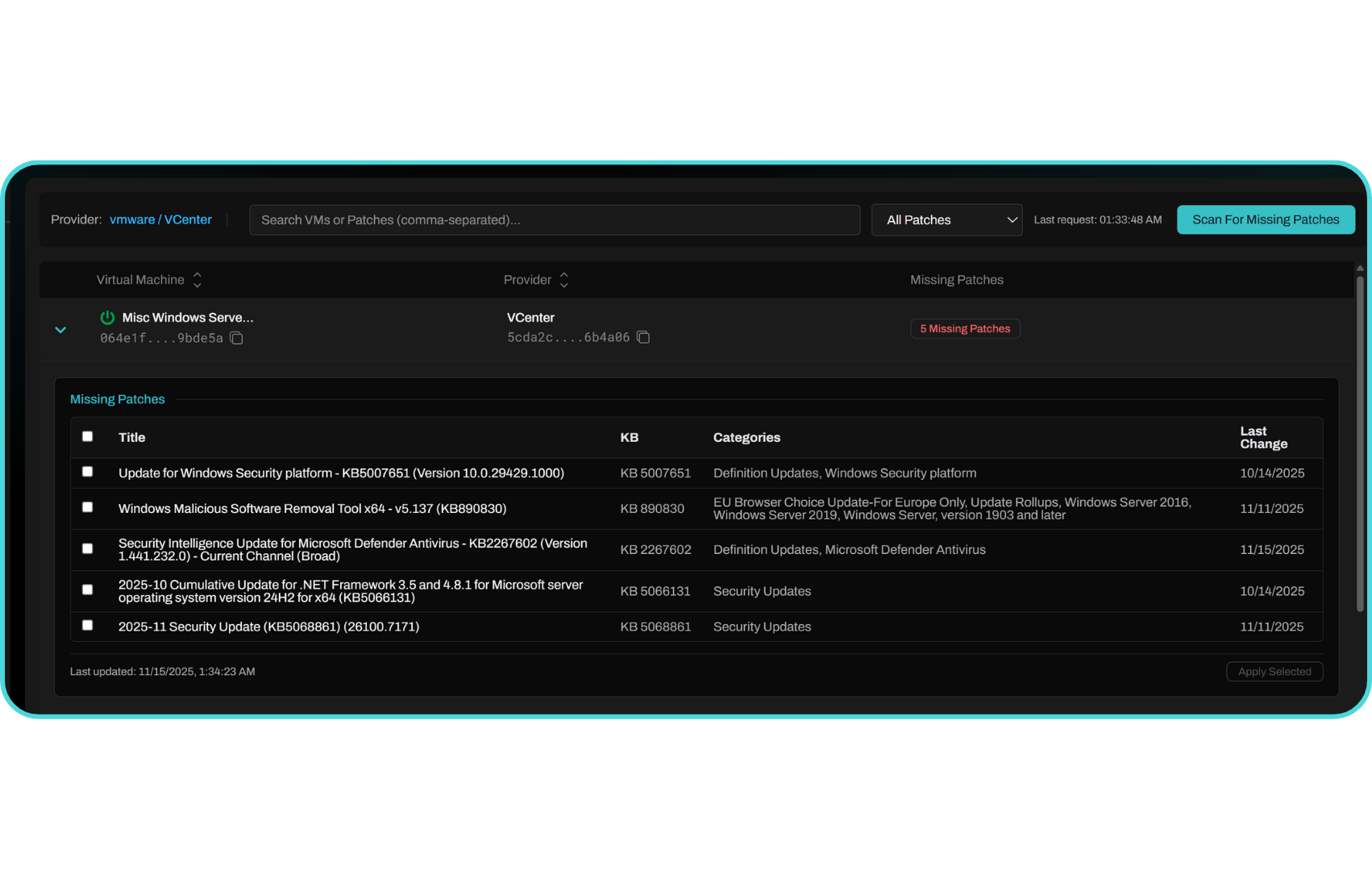
Patches
Identify and apply missing patches across Windows and Linux systems directly from Sigma’s unified interface — without agents or manual logins.
Sigma’s Patch Management capability scans your connected environments, lists all missing updates per host, and allows you to execute patching jobs across one or many machines, either immediately or on a scheduled basis.
Key Capabilities
Typical Workflow
Scan: Initiate a patch scan to identify missing updates on one or more VMs.
Review: Review the patch list with severity, size, and description.
Schedule: Choose to apply immediately or set a scheduled window.
Execute: Sigma runs the patch installation remotely using the appropriate protocol (WinRM, SSH, or guest tools).
Verify: Post-execution logs confirm success or failure, stored automatically for audit and compliance.
Note
Patch operations are agentless, executed securely over existing remote management channels. All activity is tracked in Sigma’s change history for full accountability.
Tip
Use scheduled patch jobs to align with maintenance windows and automatically document every change for compliance review.
Configuration Management
Define and enforce desired state across fleets using Sigma’s declarative configuration sets. Detect drift, preview changes, and apply idempotently with audit trails.
What You Can Manage
System Identity: Hostname, domain/workgroup, time zone, locale
Network & Name Resolution: DNS search/order, resolv.conf, hosts entries
Time & NTP: NTP servers, chrony/ntpd configuration, Windows Time service
Services & Daemons: Enable/disable, start mode, health checks (systemd/SCM)
Files & Templates: Managed files with Jinja-style templating and variable substitution
Kernel & OS Settings: sysctl, limits, SELinux/AppArmor modes, firewall policies
Windows Policies: Registry keys/values, local security policy primitives
Users/Groups & SSH/RDP: Local accounts, authorized keys, password policies
Policy Model
Declarative Sets: Versioned config “bundles” applied to tags/environments.
Variables & Secrets: Scoped values (org/env/host); secrets stored encrypted.
Preview & Diff: Dry-run to show proposed changes and per-line file diffs.
Guardrails: Can require ITSM approval or peer review before apply.
Drift & Enforcement
Watch Mode: Continuous drift detection with alerting.
Auto-Reconcile (Optional): Re-apply source of truth on drift, with rate limits and exception windows.
Evidence: Before/after snapshots, file hashes, and command outputs.
Note
All applies are idempotent. Sigma records who/what/when and links runs to tickets and releases.
Tip
Use a golden image + config set combo: keep images thin and move fast via config deltas.
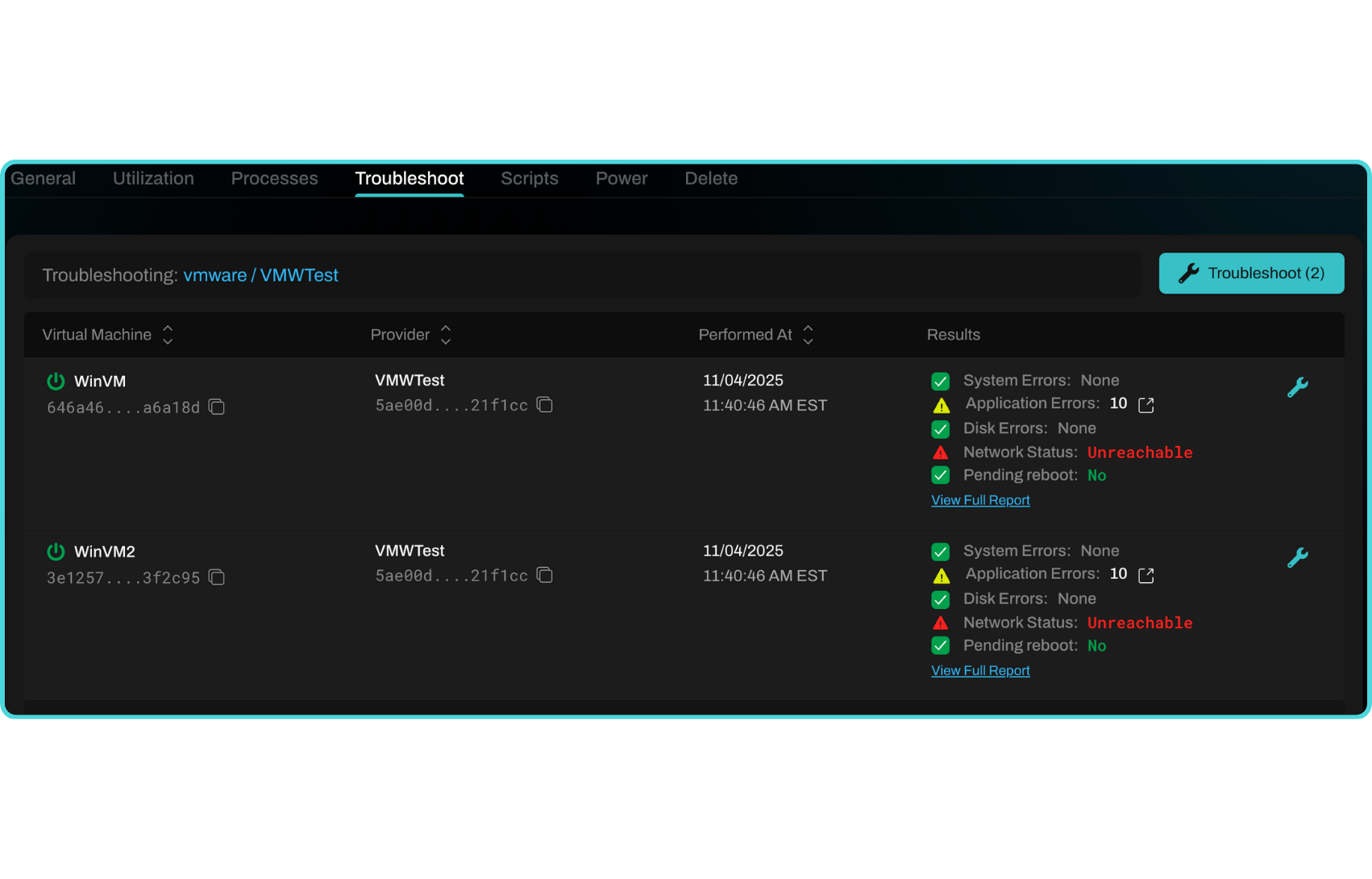
Troubleshoot
Diagnose and resolve issues quickly with guided diagnostics, data collection, and AI-assisted summaries. Launch one-off checks or full runbooks.
Built-In Diagnostics
Support Bundles
Collect logs, configs, journal/Event Viewer exports, process lists, open ports, and recent changes.
Bundle is compressed, hashed, and attached to ITSM tickets automatically if enabled.
AI Assistance
Root-Cause Hints: Summarizes symptomatic logs and correlates with recent changes or incidents.
Next-Step Suggestions: Proposes verified remediations (“increase fs.inotify, restart kubelet, rotate cert”).
Similarity Search: Finds prior incidents with matching signatures and shows what fixed them.
Collaboration
Remote Connect Tie-In: Jump straight into a live console for failing nodes; record and attach replay.
Runbooks & Task Sequences: Encode fixes as repeatable steps; require approvals where necessary.
Notifications: Push updates to Teams/Slack on state change or when human action is needed.
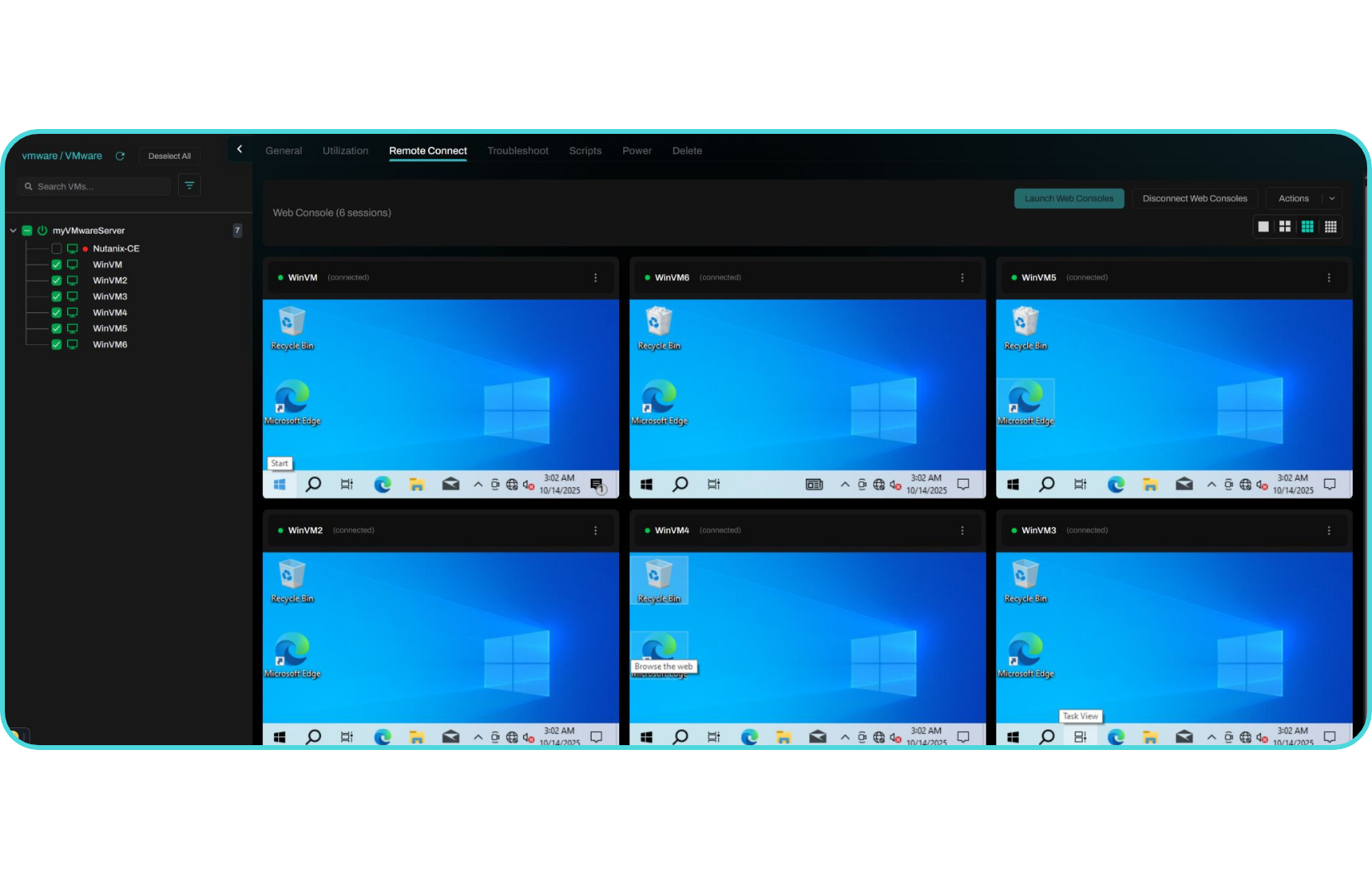
Remote Connect
Establish secure, real-time remote access sessions across one or more virtual machines, directly from Sigma’s web interface.
Sigma’s Remote Connect engine provides instant browser-based access via SSH, RDP, or native hypervisor consoles, without requiring local credentials or VPN access. Each session is fully audited, recorded, and enhanced with AI-driven analytics for replay, automation, and anomaly detection.
Key Capabilities:
AI-Enhanced Session Intelligence
All remote sessions can be recorded, analyzed, and summarized automatically using Sigma’s machine learning engine.
Every console interaction is captured as a replayable session, complete with keystrokes, screen frames, timestamps, and events.
AI summarization generates a readable summary of what happened during the session (e.g., “Patched kernel, restarted service, verified uptime”).
Event tagging automatically labels critical actions like configuration changes, restarts, or deletions inside the replay timeline.
Anomaly detection identifies unusual patterns such as mass deletions or unauthorized access attempts.
Recordings are encrypted at rest and masked to exclude sensitive input.
Collaboration and Control
Operators can collaborate and manage multiple live sessions simultaneously.
Live share: Invite teammates or supervisors to view or co-control an active session.
Observer mode: Compliance teams can watch sessions silently without user interference.
Session takeover: Administrators can assume control of a session for escalation or remediation.
Broadcast mode: Run approved commands across all connected sessions in real time.
Security and Compliance
Remote Connect enforces enterprise-grade security and detailed auditing.
End-to-end encryption (TLS 1.3) ensures all session data remains secure in transit.
RBAC enforcement limits who can initiate, observe, or replay sessions.
Session policies define maximum duration, idle timeout, and concurrency limits.
MFA enforcement for all interactive access.
Comprehensive audit trails record who connected, to which resource, and for how long, with links to recordings and AI summaries.
Integration and Automation
Remote Connect is tightly integrated across Sigma’s platform.
ITSM writeback: Attach AI summaries or session recordings to ServiceNow or Jira tickets automatically.
Task Sequences: Use Remote Connect steps as part of orchestration pipelines (e.g., validate → patch → verify).
Notification systems: Trigger Slack, Teams, or email alerts for long-running or abnormal sessions.
API access: Launch or replay sessions programmatically through Sigma’s REST or WebSocket APIs.
Performance and Scalability
Sigma’s gateway architecture supports hundreds of simultaneous connections with adaptive compression, auto-reconnect, and minimal latency. Connections automatically route through the nearest regional gateway and survive transient network interruptions without disconnecting the session.
Summary
Remote Connect transforms basic console access into a secure, intelligent, and collaborative automation layer — combining instant browser access, AI-based insight, and full auditability across any number of VMs or environments.
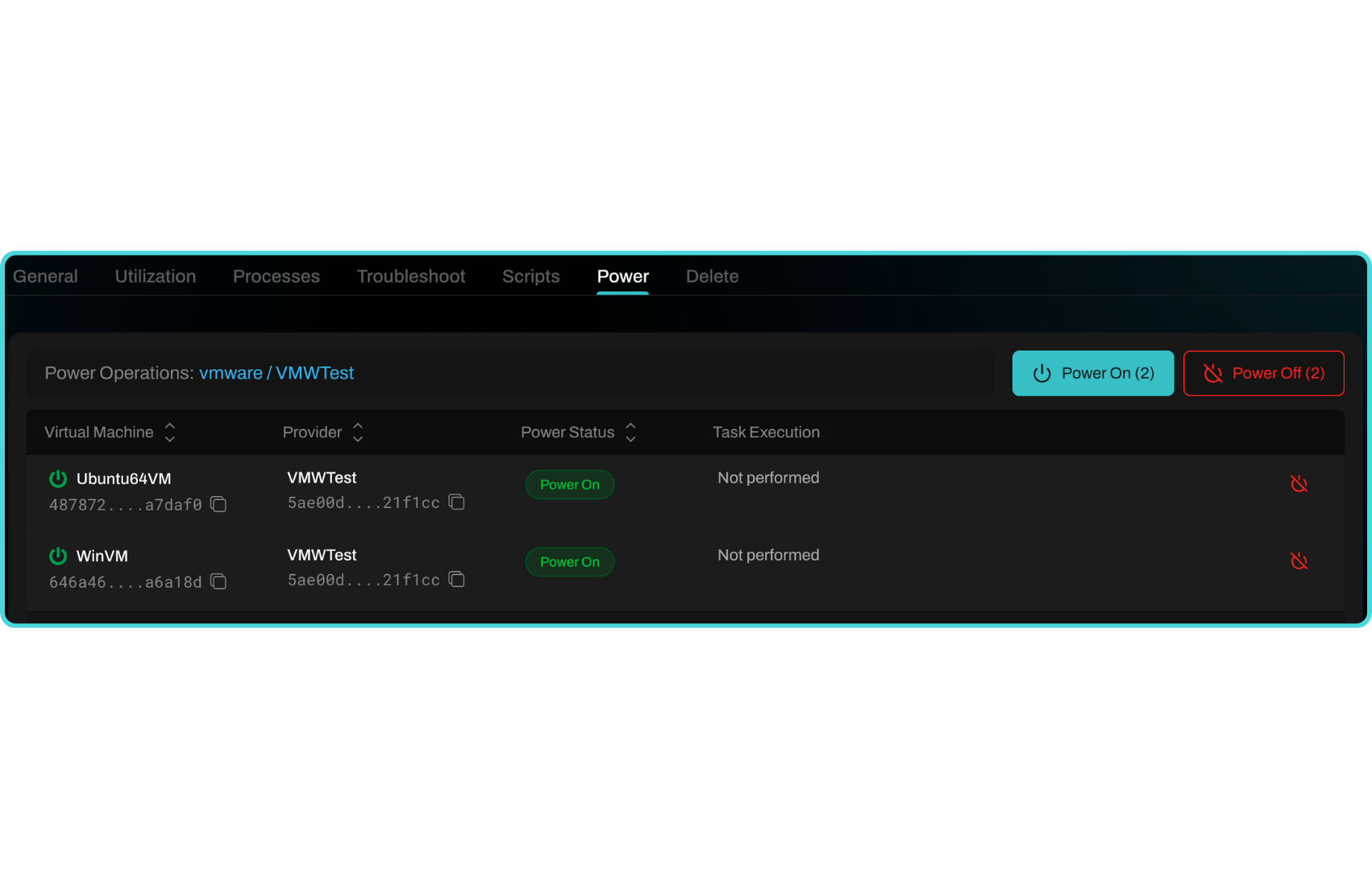
Power On/Off
Control instance power states from the UI or API.
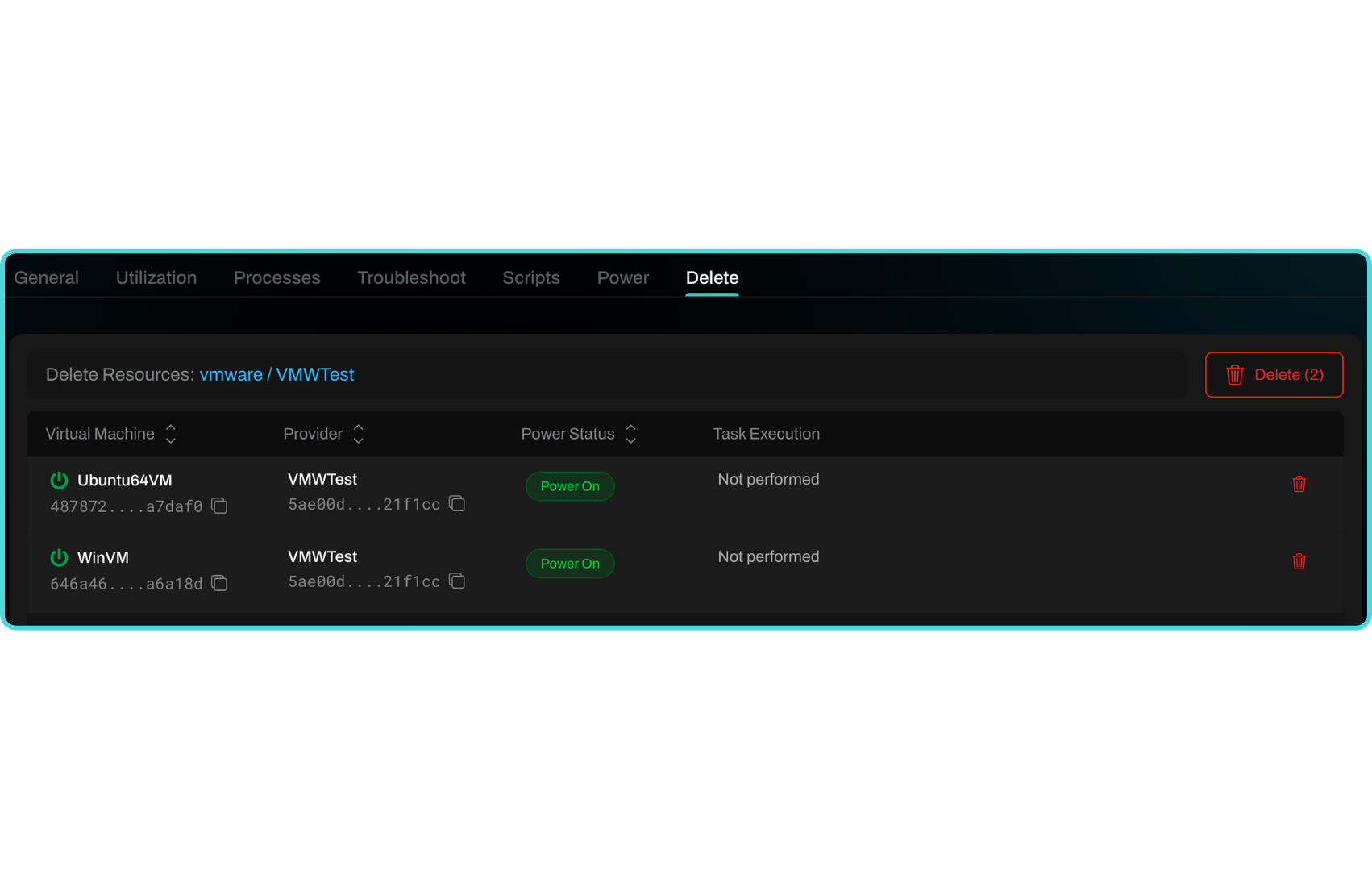
Delete
Safely decommission machines with full audit visibility.
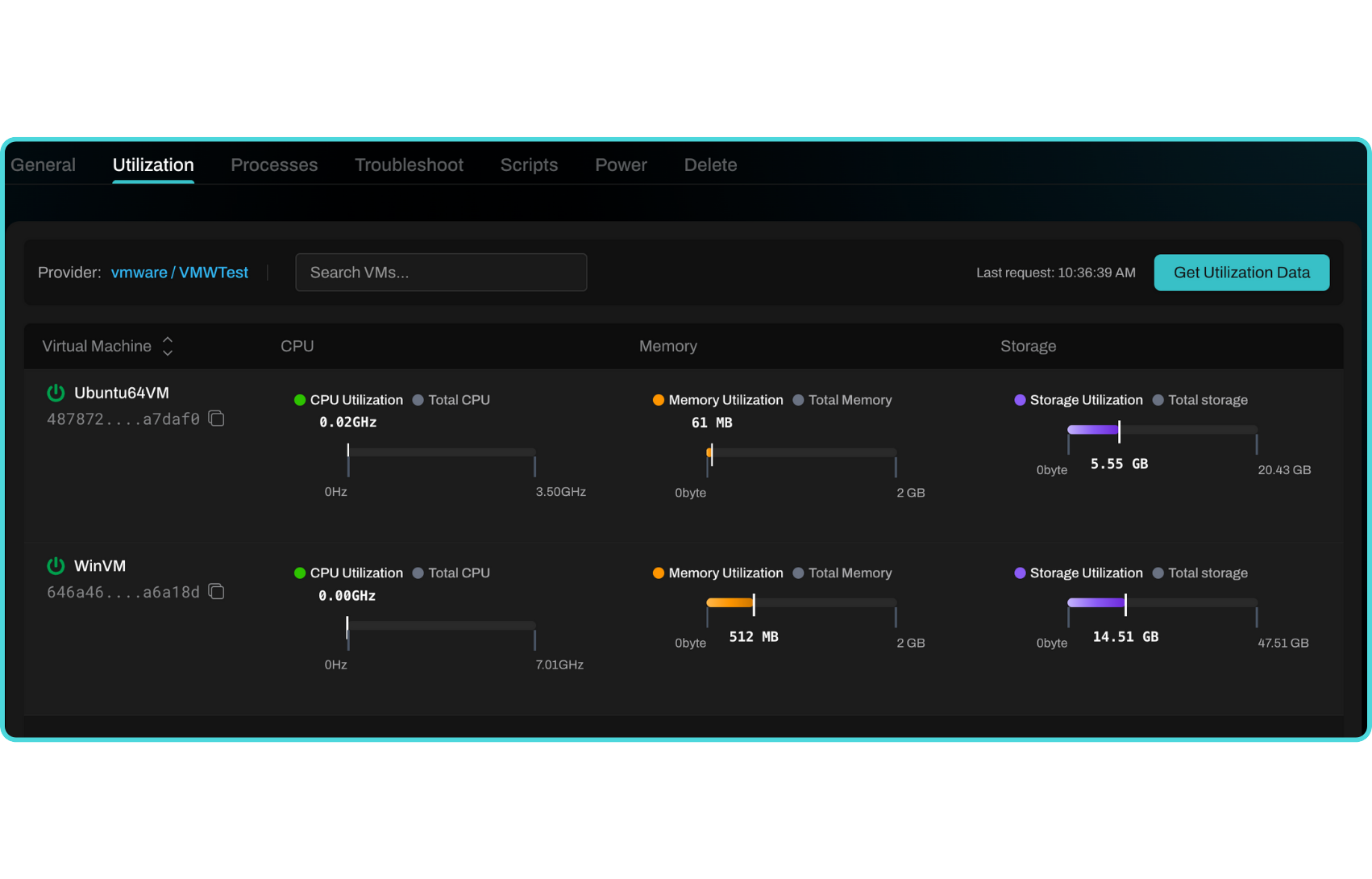
Resource Utilization
Monitor compute metrics in real time or over custom time ranges.
Metrics include:
Tip
Use resource graphs to identify underutilized workloads or noisy neighbors.
Task Sequence
Design reusable automation workflows with step-by-step logic.
Examples
Provision → Patch → Configure → Notify
Shutdown → Clone → Reboot → Apply Policy
Each step can include: - Scripts - Quick Actions - Conditional logic - Notifications
Note
Task Sequences can be triggered manually, scheduled, or integrated via API or CI/CD pipelines.
VDI
Sigma’s VDI module centralizes management, optimization, and troubleshooting for virtual desktop environments across Azure Virtual Desktop (AVD) and VMware Horizon. It enables administrators to right-size host pools, monitor session health, and automate image lifecycle management — all through Sigma’s no-code automation engine.
Note
Sigma supports hybrid VDI architectures, including Azure Virtual Desktop, VMware Horizon, and Citrix integrations (preview) — with no agents or connectors required.
VDI Quick Actions provide one-click automation for common operational tasks such as user session resets, FSLogix maintenance, and image rollouts. All actions are logged, auditable, and can write results back to ITSM systems like ServiceNow or Jira.
Important
Most VDI actions support: - Cross-platform execution across AVD and Horizon - Real-time metrics and diagnostics - AI-driven optimization recommendations - Change ticket correlation for compliance
Host Pool Management
Monitor, scale, and maintain host pools with ease.
Key Features
Host Pool Discovery: Automatically detect AVD and Horizon host pools with associated resource groups or clusters.
Dynamic Scaling: Schedule or automate scaling operations based on time of day, active sessions, or performance thresholds.
Power Management: Start, stop, or deallocate VMs intelligently to minimize idle cost.
Draining Mode: Gracefully log off users before host maintenance or patching.
Health Status View: Consolidated dashboard showing session host heartbeat, connection status, and compliance tags.
Tip
Use AI-based recommendations to identify underutilized hosts and automatically adjust pool sizes for optimal cost and performance.
User Sessions
Gain visibility and control over active user sessions.
Common Actions
View active sessions by user, host, or resource group.
Disconnect or log off problematic sessions safely.
Send in-session messages to notify users before maintenance events.
Shadow or assist sessions (where supported) for troubleshooting.
Session performance metrics: latency, CPU/memory per user, bandwidth utilization.
Note
User session actions require no direct RDP access — all operations are performed securely via Sigma APIs.
Troubleshooting and Diagnostics
Run automated tests to isolate and resolve common VDI issues.
Diagnostic Capabilities
Connection Analysis: Check gateway reachability, DNS resolution, and authentication flow.
FSLogix Profile Validation: Identify profile mount errors, corrupted VHDs, or misconfigured storage paths.
Session Log Collection: Gather RDP logs, event viewer entries, and FSLogix traces into a single support bundle.
Policy Drift Detection: Compare applied GPOs or registry values against a known-good baseline.
Tip
Combine diagnostics with a Task Sequence to auto-remediate failed profiles or reconnect users after issue resolution.
Image Management
Automate golden image creation, update, and deployment pipelines.
Image Pipeline Capabilities
Image Capture: Snapshot existing AVD or Horizon VMs as new golden images.
Image Validation: Automatically boot captured images to run smoke tests and compliance scans.
Versioning: Maintain image history and rollback capability.
Deployment: Push new images to host pools during scheduled windows with minimal disruption.
Integration: Supports Azure Shared Image Gallery (SIG), Horizon Instant Clones, and custom template repositories.
Note
Sigma can chain image builds with patching and compliance checks before publication to ensure every image is secure and standardized.
FSLogix Integration
Manage and monitor FSLogix profile containers natively within Sigma.
Features
Profile Mount Monitoring: Detect slow or failed container mounts.
Profile Reset: Clear corrupted user profile containers with one click.
Storage Health Check: Validate permissions and free space on FSLogix storage shares.
Profile Migration: Move user containers between storage accounts or file shares automatically.
Tip
Combine FSLogix management with AI-assisted analytics to identify users most impacted by profile performance issues.
Cost Optimization
Right-size and optimize VDI environments using Sigma’s AI-driven analytics.
Optimization Insights
Idle Host Detection: Identify hosts that can be powered off or resized.
Session Density Analysis: Recommend optimal host-to-user ratios based on usage trends.
Cost Forecasting: Estimate daily and monthly spend based on current utilization.
Automated Scaling Rules: Implement dynamic policies to scale in/out automatically.
Important
Cost recommendations are generated by Sigma’s AI engine using performance and utilization data — no external data sharing required.
Task Sequences
Design repeatable automation workflows for your VDI lifecycle.
Examples
Morning Startup: Power on hosts → Validate FSLogix storage → Notify users.
Patch Cycle: Drain sessions → Apply updates → Reimage → Resume pool.
User Remediation: Detect failed profile → Reset FSLogix → Reconnect session.
Each sequence can include: - Power actions - Scripts (PowerShell, Bash) - Condition checks - Notifications to ITSM or Teams/Slack
Note
Task Sequences can be scheduled, triggered by monitoring alerts, or invoked manually for on-demand maintenance.
Reporting and Compliance
Generate detailed reports on VDI usage, cost, and compliance.
Session Audit Logs: Track who connected, when, and from where.
Change History: Record configuration and image changes across all environments.
Resource Utilization Reports: Highlight over/under-utilized hosts and user activity peaks.
Export Formats: CSV, PDF, or JSON for governance and review.
Tip
Combine with Sigma’s ITSM integration to automatically attach usage or cost reports to ServiceNow or Jira change tickets.
Orchestration
The Orchestration interface enables users to define multi-step workflows that automate infrastructure tasks across environments. Each step in an orchestration can execute a predefined task on a selected environment, and logic-based components, such as delays and decisions, can be added to control the execution flow.
Overview
Orchestration is composed of sequential steps. Each step includes the following settings:
Select Environment Type – Choose the type of environment (e.g., Compute, ITSM, AI).
Select Environment – Choose from the list of connected environments within the selected type.
Select Task – Choose the action or task to be executed in the selected environment.
You may add multiple steps to build complex automations.
Building a Workflow
Click the + icon to add a new step.
For each step: - Select the Environment Type (e.g., Compute). - Choose a connected environment from the dropdown (e.g., vcenter-lab). - Select a task from the available task list.
You can collapse, remove, or reorder steps using the icons located at the top right of each step panel.
Toolbox: Delay and Decision
On the left side of the screen is the Toolbox, which allows you to drag logic controls into your orchestration:
Delay – Pause workflow execution for a defined duration before continuing to the next step.
Decision – Introduce conditional branching based on the output of previous steps. This enables dynamic flows within your orchestration.
Execution Logs
On the right-hand panel, you can view the status of the orchestration:
Current – Shows active orchestration runs and their real-time progress.
History – Displays previously run orchestrations, including step results and timestamps.
Saving and Loading Orchestrations
At the top-right of the interface:
Click Save Orchestration to save your current workflow for future reuse.
Click Load Orchestration to retrieve and edit a previously saved workflow.
Validation
Before execution, ensure all required fields in every step are completed. A warning bar at the top will indicate if any step is incomplete.
Builds Wizard
The Builds module in Sigma Automate provides a streamlined, guided workflow for provisioning and customizing virtual machines across cloud and on-prem environments. Whether you’re building a new VM from scratch, migrating an existing workload, or standardizing VM templates across environments, Sigma’s intuitive, step-by-step process ensures consistency, compliance, and operational efficiency — all without requiring deep infrastructure knowledge.
Note
Sigma’s Builds module supports major hypervisors and cloud platforms including VMware vSphere, AWS, Azure, and OCI. The workflow is platform-aware, allowing for intelligent defaults and provider-specific configuration options.
Key Use Cases
Provision New VMs Spin up virtual machines based on a consistent, policy-driven template. Teams can define compute specs, OS images, storage, networking, and post-provisioning configuration through a single UI or API.
Migrate Existing VMs Use the build process to migrate workloads from one environment to another (e.g., on-prem VMware to cloud). Sigma supports importing existing configuration parameters and applying them to new destinations, minimizing downtime and manual reconfiguration.
- Standardize Environments
Input how many VMs you want to create. The allowed range is from 1 to 50.
Enter VM name: Define the base name. Sigma will automatically append numbers if you’re creating more than one VM (e.g.,
web-serverbecomesweb-server-01,web-server-02, etc.)VM Names Table (Preview): Once you enter the values above, this section populates dynamically to preview VM names and numbers.
Destination Environment * (Center Panel)
Choose where the build should be deployed.
Build Destination Environment: Select from a dropdown list of available environments (e.g., Production, QA, Dev, Edge).
Target Location: This area displays the full path or infrastructure segment where your VMs will reside (populated automatically after environment selection).
Build Type * (Right Panel)
Choose how to start your build:
New (Default): Begin the configuration from scratch. Ideal for custom or one-off deployments.
From Template: Use a previously saved VM build template. This pre-fills the configuration based on saved values from earlier builds.
Actions (Top Right)
Save Build: Saves current selections and configurations for later use.
Load Build: Opens a saved build to continue or reuse.
Notes and Tips
Fields marked with an asterisk (*) are required.
Hover over the yellow info icon (!) to get in-context help.
Templates help enforce standardization across teams and environments—use them to reduce errors and save time.
Ensure the environment selection aligns with your deployment region and compliance requirements.
Navigation Controls
Click Next to proceed to Step 2: Select Operating System, where you will define the OS for your VMs.
Step 2: Operating System
In Step 2 of the VM build workflow, you will select the operating system (OS) or base image to install on the virtual machines. This step ensures your VMs are provisioned with the correct system environment.
Sections on This Screen
Supported Operating Systems *
Choose from a list of common OS families. Each option represents a category of available base images.
Available OS options:
Windows - All Windows Server versions and client builds (e.g., 2022, 2019, 10)
Ubuntu - Popular open-source Linux distribution for developers and cloud workloads
Red Hat - Enterprise Linux distribution for secure, stable environments
Mac - macOS images (typically available only in specific hardware-licensed environments)
Marketplace - Community and partner images available via your cloud provider’s marketplace (e.g., hardened OS builds, DevOps tool images, etc.)
Tip
Hover over each OS tile to view version availability or licensing notes, if supported in your environment.
Select OS/Image
After choosing an OS family, this dropdown (or secondary list) will populate with specific versions or custom images available in your environment.
Examples:
Selecting Windows may present: - Windows 10 - Windows 11 - Windows Server 2022
Selecting Marketplace may display: - Bitnami Jenkins Stack - Palo Alto NGFW VM-Series - CentOS 7 Hardened
Navigation Controls
Previous - Go back to Step 1: Select Details
Next - Proceed to Step 3: Select Compute Resource (only enabled after choosing an OS/Image)
Notes and Best Practices
Fields marked with * are mandatory
The Marketplace section requires appropriate cloud permissions to list or deploy third-party images
Use organization-approved custom images when available to align with internal compliance policies
Some OS choices may affect downstream options in hardware, storage, or licensing
Common Use Cases
Use Case |
Suggested OS/Image |
|---|---|
Windows-based application hosting |
Windows Server 2022 |
Linux-based web development |
Ubuntu 22.04 |
Legacy system compatibility |
Red Hat Enterprise Linux 7 |
Testing with third-party tools |
Marketplace images |
Step 3: Compute Resource
Assign the compute resource that will host your virtual machines. This determines the physical or virtual host cluster where the VMs will run.
Sections on This Screen
Compute Resource Selection *
Choose the appropriate compute resource for this build from your organization’s available infrastructure.
Tree View Navigation:
Displays a hierarchical view of available data centers and compute nodes.
Example:
ha-datacenter └── esxi01.acmecorp.com
Click on the desired compute node to select it. This selection determines the hypervisor or cluster that will host your VMs.
Compatibility Check Panel
After selecting a compute node, Sigma automatically runs compatibility checks to verify whether the selected OS, VM specifications, and resource requirements can be met.
Success: “Compatibility checks succeeded.”
Failure: Error messages will indicate issues like CPU generation mismatch, insufficient memory, or unsupported features.
Navigation Controls
Previous - Select Operating System
Next - Select Storage (enabled only after a compatible resource is selected)
Notes and Best Practices
Choose compute nodes based on location, workload capacity, and compliance requirements
Compatibility validation helps prevent common provisioning failures by detecting hardware mismatches or unsupported configurations early
The system may auto-filter hosts that do not meet the minimum requirements
Example Use Cases
Scenario |
Recommended Action |
|---|---|
You need VMs on a specific ESXi host |
Select the corresponding node (e.g., esxi01.sigma-automate.com) |
Building VMs in a DR site |
Navigate to the appropriate secondary datacenter branch |
Target node fails compatibility check |
Choose an alternate compute resource or modify VM specs |
Step 4: Storage
Assign a datastore to hold the virtual machine files (e.g., OS, application binaries, VM snapshots). This ensures sufficient space and the correct type of storage for your VM workloads.
Sections on This Screen
Datastores *
This section displays all available datastores accessible from the compute resource.
Each datastore is listed with the following attributes:
Datastore Name - The label identifying the storage target (e.g.,
datastore1)Datastore Type - Type of file system (e.g.,
VMFS,NFS, etc.)Datastore Free Space - The available capacity in gigabytes (e.g.,
197.49 GB)
How to Use:
Select a datastore by clicking the radio button beside it.
Only one datastore can be selected per VM build.
The Next button becomes active after a valid selection is made.
Selection Criteria & Recommendations
Criteria |
Guidance |
|---|---|
Available Space |
Ensure the free space exceeds the total estimated VM size. |
Performance Tier |
Choose SSD-backed storage for high-performance workloads. |
Redundancy |
Prefer datastores backed by fault-tolerant or RAID-configured arrays. |
VMFS vs NFS |
VMFS is optimized for VMware-based VMs; NFS is suitable for shared access. |
Navigation Controls
Previous - Returns to Step 3: Select Compute Resource
Next - Proceeds to Step 5: Customize Hardware
Notes and Best Practices
Fields marked with an asterisk (*) are required.
Insufficient space or unsupported datastore types will prevent VM provisioning.
If no datastore is available, verify permissions or go back to select-storage and select a different compute resource.
Example Use Case
If you’re deploying a development VM that needs around 100 GB of disk space:
Select a datastore with at least 150-200 GB free to allow for logs, snapshots, and system overhead.
In this case:
datastore1with 197.49 GB of free space is acceptable.
Step 5: Hardware
Define the virtual hardware specs for your VM—specifically CPU and memory. This step helps ensure the VM is provisioned with the right amount of compute power for its intended workload.
Supported Hardware
Configure your VM’s virtual CPU and memory allocation.
Hardware Types:*
Type
Setting Fields
Description
CPU
Count: Number of vCPUs
Ratio: CPU overcommit ratio (e.g., 1:1, 2:1)
Compatibility dropdown
Assign compute processing power. Higher vCPU counts improve performance for CPU-intensive workloads. Flag for hardware compatibility with selected compute node.
Memory
Size: RAM in MB or GB
Compatibility dropdown
Memory allocation for the VM. Ensure it meets workload needs. Similar compatibility flag as with CPU.
Warning
If compatibility is flagged as False, check the selected compute node (Step 3) for resource availability or reduce CPU/Memory requests.
Configuration Panel (toggle to enable advanced hardware settings)
Customize Advanced Configuration
When enabled, additional fields may appear for:
NUMA settings
Virtual device passthrough
Boot order configuration
Hardware acceleration support (e.g., nested virtualization)
Best Practice Guidelines
Scenario
Recommendation
Lightweight utility VM
1 CPU, 512 MB - 2 GB RAM
Web or app server
2-4 CPUs, 4-8 GB RAM
Database server/analytics
4-8 CPUs, 16+ GB RAM
Enable advanced config
For performance tuning or hardware-specific features
Notes
All fields marked with an asterisk (*) are required.
Hardware settings must pass compatibility checks based on the compute resource selected.
The platform may offer guardrails or display warnings if the requested specs exceed available resources.
Step 6: Configuration
This step provides advanced configuration options for finalizing how the virtual machine is initialized, connected, secured, and provisioned. It includes five tabs:
Tabs & Fields
Authentication *
Define how local credentials are configured for initial access.
Use Sigma-generated SSH key - Toggle to auto-generate and inject SSH credentials.
Autologon - Enable automatic login on VM startup (for Windows).
Local Username - Required field; initial login user.
Local Password - Required field; ensure strong password policies.
Organization Name - Optional label for licensing or compliance tagging.
Domain (Windows only)
Allows the VM to join a domain automatically at boot.
Domain Join (toggle) - Enable to join a domain.
Domain Name - FQDN (e.g.,
corp.internal.local)Domain User - User account with permissions to join machines to the domain.
Domain Password - Password for the above account (stored securely).
Note
Domain join typically requires that networking be configured correctly (see the next tab).
Network (Optional)
Configure a static network assignment if DHCP is not used.
Network Configuration (toggle) - Enable to manually configure.
Subnet - Select from predefined network segments.
IP Address - Assign static IP.
Subnet Mask - Typically
255.255.255.0.Gateway - Default gateway IP.
DNS Domain - e.g.,
internal.company.comDNS Server List - Comma-separated list of IPs (e.g.,
10.0.0.2,10.0.0.3)
Task Sequence (Optional)
Specify a pre-configured automation workflow to run on the VM.
Task Sequence (toggle) - Enable to attach a predefined automation runbook.
Task Sequence dropdown - Select from available sequences (e.g.,
InstallPatches,InitializeDatabase,BaselineConfig)
Tip
Used to auto-install software, apply security policies, or run provisioning scripts.
User Data (Optional)
Insert raw initialization scripts to execute on first boot.
Script Language - Choose from Bash, PowerShell, etc.
User Data Script - Paste the script here. Supports base64 encoding for cloud-init.
Hint
This is ideal for advanced IT automation workflows or cloud-native provisioning.
Navigation Controls
Previous - Customize Hardware
Next - Confirm and Review
Notes
Fields marked with an asterisk (*) are required to continue.
The more configuration options you use, the more automated the provisioning becomes.
Use Task Sequences or User Data if integrating with CI/CD or compliance baseline requirements.
Ensure consistency with internal IT policy for domain credentials and networking standards.